eCommerce
Advice for Connecticut Businesses Using WordPress to Avoid Getting Hacked
Posted on .Do You Know Where Your Hackers Came From?
The troubling statistic is the most people do not know how the hackers have entered through their site. According to a WordPress survey, 1,032 respondents took the survey, but 61.5% did not know how the hacker gained access to their website. But, many of these people also cleaned their sites themselves, which is not recommended.
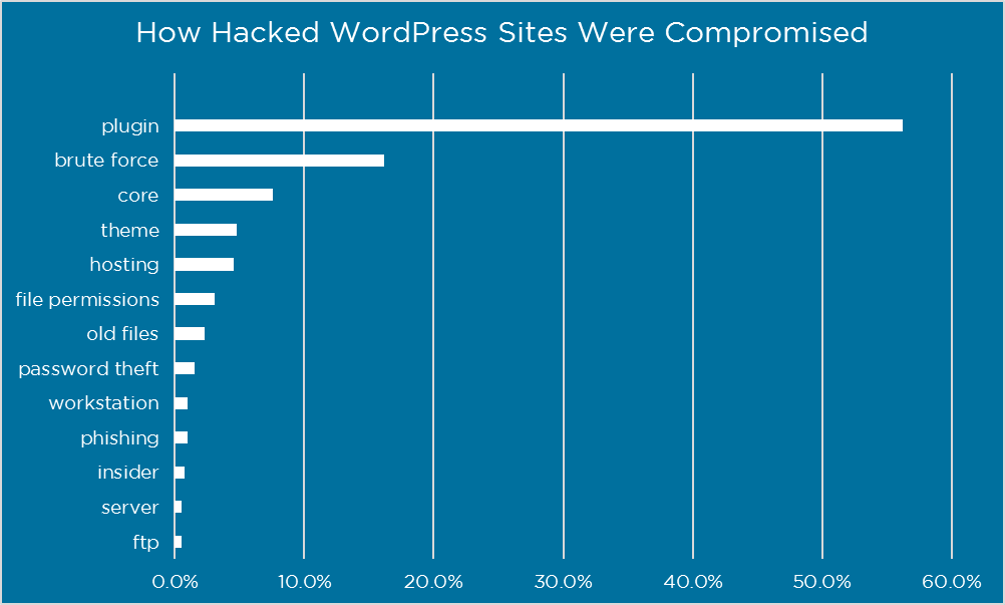
From the survey respondents who did know where the hackers came from, and the information is in the chart below:
Plugins
Plugins are a risk since there are 43,719, making it a big part of the WordPress website. But, according to Wordfence, plugins were responsible for 55.9% of unknown entry points by respondents. It is important to keep all plugins up to date to fix issue before hackers can get into your site. Do not use abandoned plugins, and make sure non WordPress plugins have sites that are reputable. Also make sure that there is always an active author updating plugins to make sure there are no bugs.
Brute Force
Brute Force is when the hacker will get the information for your username and try to guess your password. There is password hacking technology that can be 100% effective. This style of hacking is a problem for WordPress users, representing 16.1 % of any known entry points from survey respondents.
Here are some tips for Preventing a Brute Force Attack:
Signing in With Your Cell Phone
The user must have their username and password, but also have possession of their cell phone. This is 100% reliable in preventing a Brute Force attack, and is available now with Wordfence.
Refrain From Using Easy-to-Guess Usernames
Usernames like ‘Admin’ or ‘Administrator’ are the most targeted accounts. These are the ones that are the most hacked and easiest to hack by Brute Force. Also, do not use your company name, Domain name, or workers names as usernames.
Sign Up For Login Security in Wordfence
By enabling security login on the free version, you will get tons of features such as:
- Strong passwords
- Locking users after limit to number if login failures is exceeded
- Locking out wrong username attempts
- WordPress cannot reveal correct usernames in login errors
- Inability to show username through author scans
- Locking IPs attempting to sign in as defined list of usernames
Comments are closed.